Cloudflare Zero Trust, MFA Hardening, and Pterodactyl
Let's pretend you're the sysadmin for a major government institution, or perhaps for a multi-billion dollar company; you have tons of admin portals (publicly exposed to the internet, of course), and need to secure them from attack. There are many ways to skin the cat per-say; you could setup a VPN, or maybe configure geo-IP fencing, or maybe even change your mind and stop exposing it to the web.
BUT, there is another way to go about doing this; Cloudflare Zero Trust.
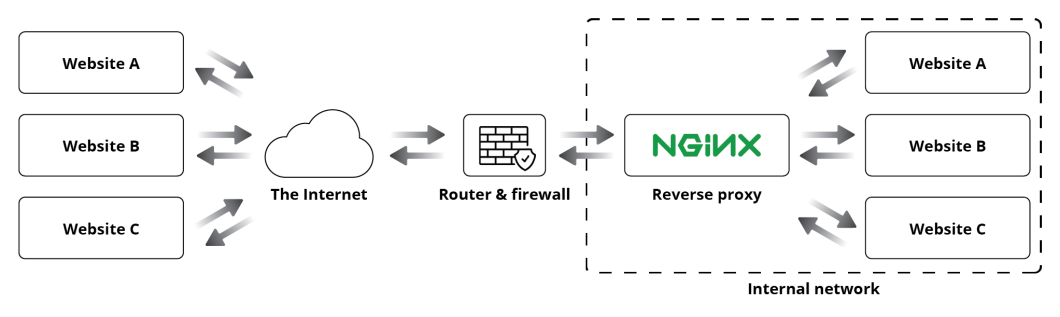
Cloudflare Zero Trust is like a one-stop shop; it offers proxying, web server gateways, VPN connectivity, and data protection all in one package.
Cloudflare Zero Trust
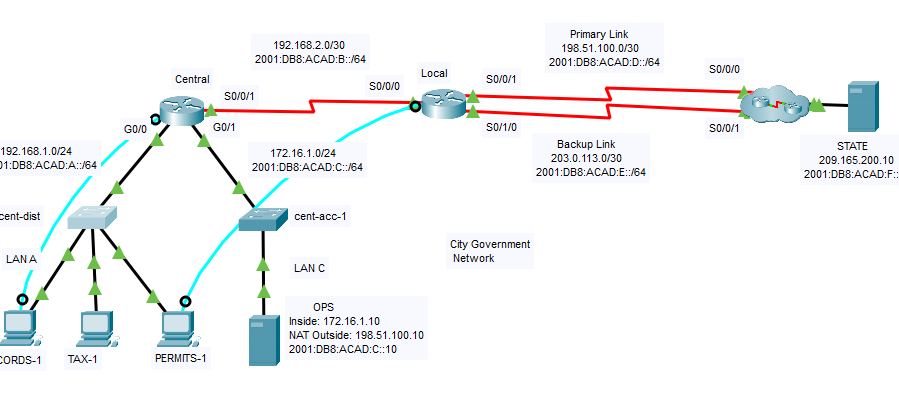
For the longest time, even since Lab 1.0 I've been using some kind of NGINX reverse proxy service to get my applications available on the web from inside my network. It makes it simple; Setup DNS records, bring up app, configure proxy rules, presto - live.
While this is an excellent solution, it has a few issues:
- I can't really secure applications without introducing another layer of complexity into the mix. Think Authelia, Keycloak, Authentik, etc. I don't want to do that because it creates another place for things to go wrong. I just want to be able to sign into my apps, without thinking too much about it.
- I have to rent a VPS to host my reverse proxy on; as previously written, by hosting my reverse proxy on a VPS, I can put a "shield" of obscurity on my traffic so that people can't 1-2-find out who my ISP is, or where I live.
- It feels like a crutch, NGINX Proxy Manager has a nice GUI, but it limits you with what it can do. Sure you can go into CLI and do it all from there, but some changes don't persist, or simply just don't work.
I've seen tons of articles, posts, or even gotten messaged about using Cloudflare Zero Trust in the past. I've been hearing about it since it was originally named Cloudflare Argo, or Cloudflare Tunnels. (Before it evolved into Zero Trust)
While they looked compelling, I personally wanted to try to stay away from being dependent on a company for these types of things. However, I eventually caved.
It accomplishes alot of the things I wanted to change about my setup:
- It masks my traffic, protecting me and my network from potential snoops and attacks.
- It provides a secure gateway to sensitive applications with SSO using Microsoft Entra ID (With Cisco DUO MFA)
- It's easy to spin up, move around, and configure. Most of it's configuration is done via the Cloudflare Zero Trust admin panel, hosted by Cloudflare.
- It also doubles as a VPN to my homelab, I can open up Cloudflare Zero Trust on my desktop, or Cloudflare One on my smartphone and connect in an instant to my local network fileshares or my remote desktop.
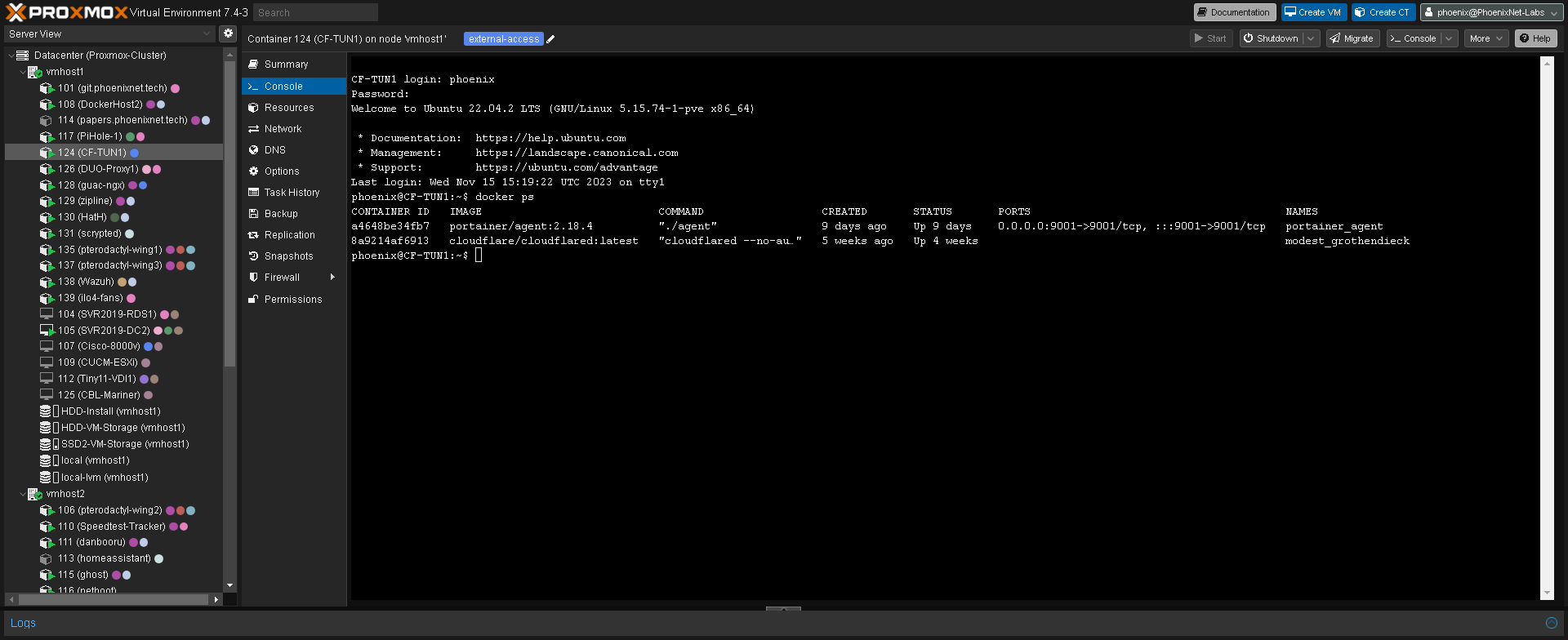
Setup took me ~1hr to migrate my DNS records, spin up a LXC container in proxmox, and install Cloudflare Daemon in a Docker container. Not too bad!
I've been using it for ~4 months at this point, and I'm pretty satisfied with it. It has a few things I'd wish were better. Guacamole stutters pretty bad over Cloudflared, but that's something I don't mind continuing to host a proxy for, as Cloudflare also strictly prohibits video transmission through Cloudflared as well.
MFA Hardening
On the topic of security improvements, MFA is a huge deal right now. Passwords are as weak as putting a Cheeto in your door jam and the best way to combat that is setting up MFA for literally everything possible.

Whenever I setup an application in my lab, I try to integrate SSO. This keeps the number of unique passwords I have to remember down to a minimum, and avoids confusion. Typically, I either integrate LDAP or Microsoft Entra ID since both have support for DUO MFA.
At work, we've implemented what DUO calls the "LDAP Proxy Service" which is an application that runs on either a Windows Server VM, or a Linux Server VM/LXC. I chose the latter, because Linux is light, and LXCs are like a feather in comparison to a full-blown Windows Server VM.
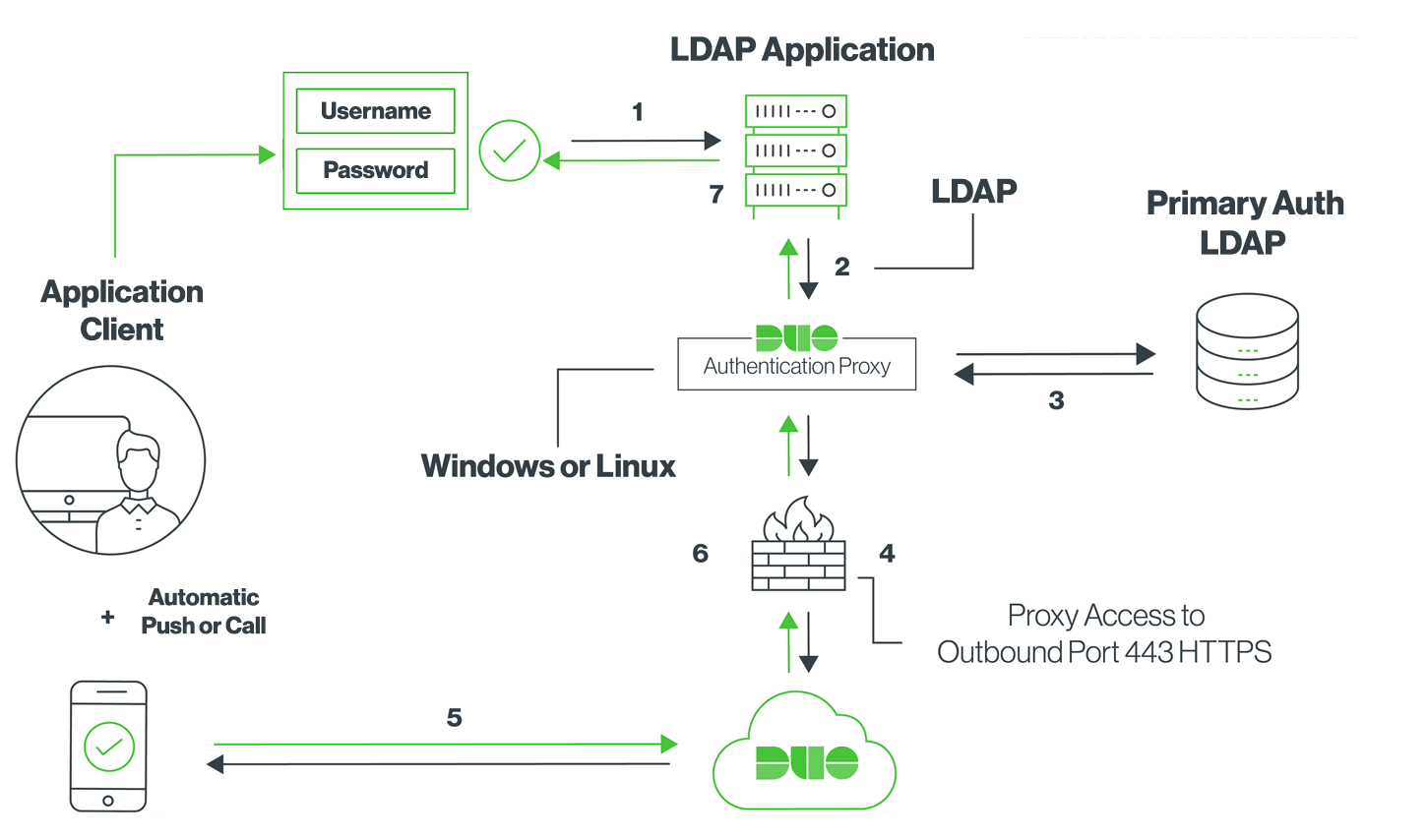
After doing my research, I deployed a HA (please, don't roll just one, there's nothing worse than getting locked out by your own security) cluster of 2 LXCs running the DUO LDAP Proxy, and pointed a few applications at it vs. directly at my AD Domain Controllers and tested things out.
With a DUO LDAP Proxy, it doesn't show anything "graphical" to the user, but before permitting login it sends a push to their phone. When the user accepts the push, the login completes and the application proceeds to the next screen.
This is a game changer, as you can put MFA on literally anything now, as long as it supports LDAP. Applications like Portainer, Gitlab, or Netbox that don't offer DUO as a direct integration can be secured without modifying / installing integrations.
Pterodactyl
From the beginning, the number one reason I ran a "server" or "hosted" was for running game servers. I didn't want to play on somebody else's terms, or be annoyed when they had to go down for maintenance. I wanted full control, and sub 5ms latency while I was at it.
I've used a variety of solutions, ranging from manually running game servers, to Cubecoders AMP. Each application has their own problems, mostly breaking when updating or just annoying me in some way or another.
Previously, I'd been using AMP, as it met my needs, and the licensing was cheap at only $15 for a lifetime license. However, I like to run my game servers in a clustered configuration. One LXC for the management panel, and multiple LXCs to split the load of running multiple game servers at once.
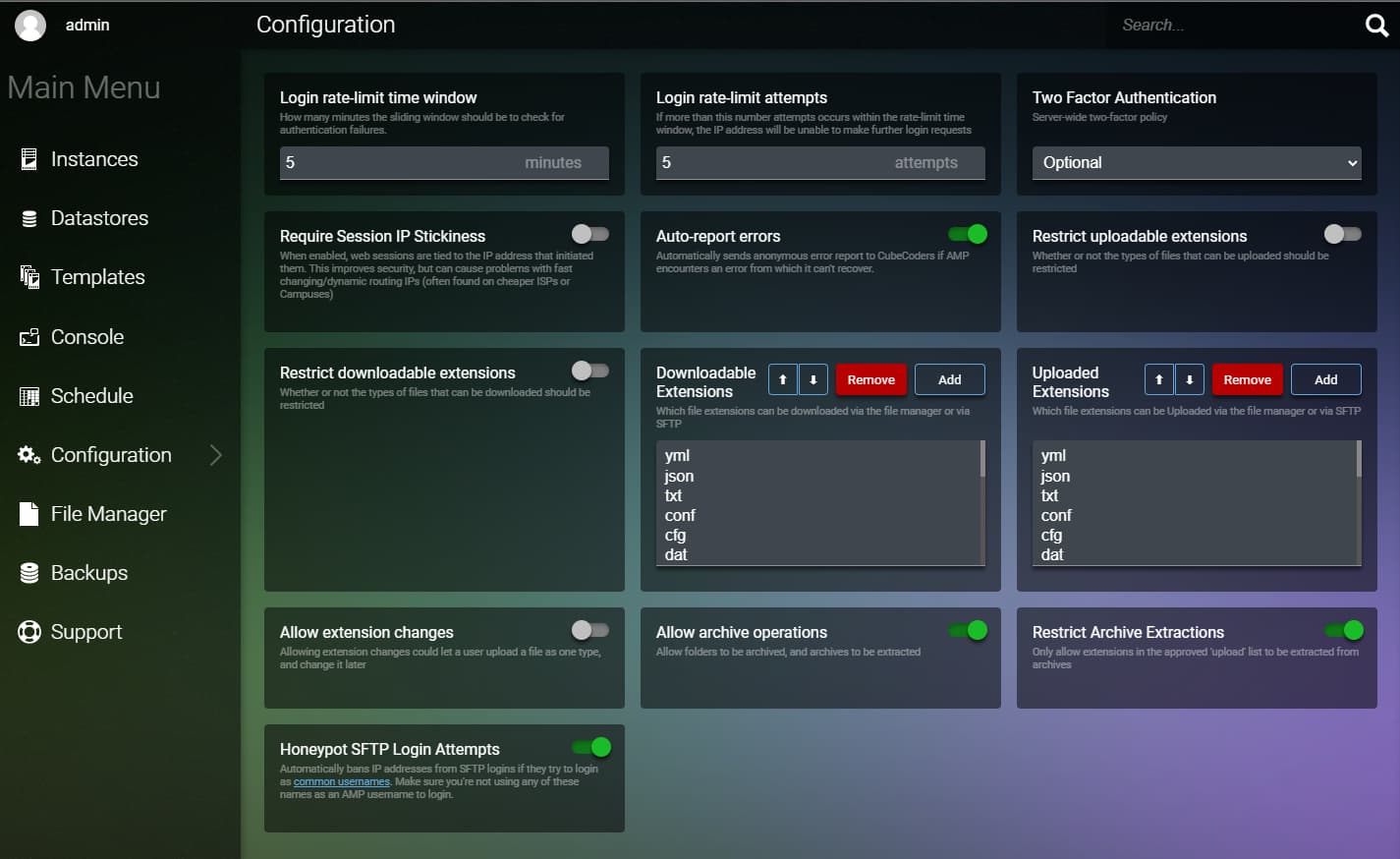
Whenever I updated AMP, it would break authentication between these "nodes" in the cluster, and ultimately derail the whole thing. Their community support was pretty lackluster, blaming it on me, and my setup. After reinstalling 2-3 times across multiple derailments, I eventually decided I had enough and moved on.
I've considered using Pterodactyl in the past, as it looked nice and I really liked the appeal of running it in docker, but it just seemed so daunting. After doing a ton of research, I finally pulled the trigger on it and deployed a simple 2-node setup to play around with. Ran a few Minecraft servers on it, and I really liked it.
![How To Install Pterodactyl Panel [EASY INSTALL SCRIPT] - GhostCap Gaming](https://www.ghostcap.com/wp-content/uploads/2021/01/Pterodactyl.png)
Migrating data over wasn't too bad either, just drag and drop via SFTP to the server via the credentials provided in the admin panel.
They even have support for custom theming, I wasn't a huge fan of the default theme they provide, it really screams "Free Bootstrap 3 Web Panel" whenever I look at it. I went with a nice modern looking theme and it wasn't too bad to apply.
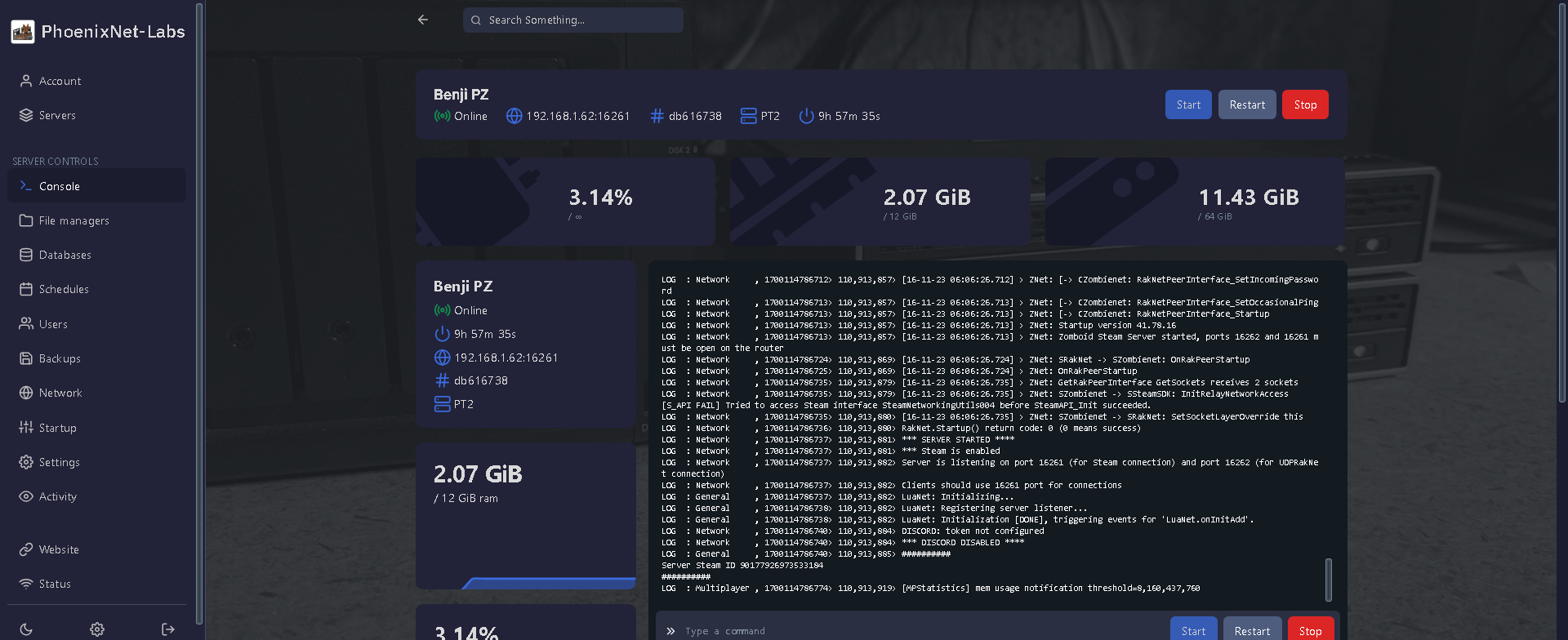
All-in-all, I'm really happy that I migrated over to Pterodactyl from AMP, I personally didn't opt to use anything like LDAP or MFA, but I also just slapped Cloudflare Zero Trust on it and called it a day.
Notes to the audience
Hi there, sorry if it's been a while. I've been dealing with a whole barrage of issues lately. Sometimes life can deal you a bad hand, and you kind of just "have to cope" with it.
In June of 2023, I was diagnosed with a benign tumor in my groin, and it significantly impacted my life for a little while. Movement was tough, performing my daily activities was grueling and I just really lost my motivation. My doctor(s) had a hard time determining what it was at first, suggesting all kinds of things until ultimately an MRI determined what it was. Doing all of this testing drained me both physically, and financially. Projects got put on hold, my "hobby fund" dried up and ultimately I decided to freeze everything for the time being.
Since then, I've had surgery to have it removed, and have made significant progress on improving my health. Things are somewhat back to normal, with my physical restrictions removed, and I can resume normal activities again. But my mental health also took a bit of a hit in the crossfire.
Writing these articles on my adventures is really something I enjoy; it helps me document my findings, share my passion with the world, and provide to potential employers the extent of my knowledge. When I'm not feeling my best, I really turn into a bit of a shut-out and lose my steam.
I thought I'd come back to writing these articles again to maybe motivate myself to keep improving. I've done a few things since things cleared up for me, like setup CF ZT, or MFA Hardening, or even Pterodactyl but there's just so much more I want to do.
I've got some new projects in the works; A New NAS, A New Flash NAS, Full 10GB Connectivity, etc. But those are some distant goals right now, as I'm focusing on paying medical debt and improving on another aspects of my life right now.
Not trying to get all personal with whoever you are reading this, but I just thought I'd share on "where the hell did OP go" or whatever.
Thanks for reading,
And until next time...