Expanding on the satellite location deployment project
Previously, I discussed setting up a site-to-site VPN, deploying a DIY NAS and equipping my dad with the tools to login and access my lab remotely from afar.
After doing some testing, and determining that absolutely nothing I deployed was going to work, I had to make some changes to my plan.
Synology Redux:
After reviewing how the DIY TrueNAS setup performed, I quickly realized this wasn't going to work for a number of reasons:
1: The "NAS" was a bit hodge-podged together, using spare parts I had (2TB constellation drives leftover from the old lab, a PERC H710 I flashed to IT mode, and my dad's old desktop PC). My dog kept bashing into the side of it, causing drive(s) to fail as there wasn't really a good location to store it other than on the floor.

2: There isn't an on-site AD domain controller available, which makes LDAP/AD authentication a nightmare. This isn't necessarily a bad thing, I don't really like the idea of managing a 3rd DC, not to mention it's not necessary with the site-to-site VPN being available.
3: His login is AzureAD only, which prohibits him from authenticating against local AD/LDAP. This was a major issue I ran into, I couldn't setup SMB shares to authenticate against because he wasn't in the AD DC to begin with.
I decided to revamp the whole shebang to remediate all of the above issues.
After discussing his needs in terms of storage and capability, I was able to narrow things down to a few requirements:
A) 4TB minimum of storage.
B) It needs to be simple to manage, fix, and reboot. He's not an IT professional, he's an IT enthusiast. I can't expect him to be able to troubleshoot anything in the event anything doesn't work.
C) It needs to be low-power, and able to be tucked away out of sight.
(Small, Quiet, etc.)
Introducing, the Synology DS220j
After discussing some options, QNAP, ASUSTOR, etc. I personally recommended what I use in my lab to him: a Synology DiskStation.
He expressed that he didn't want any of the fancy features that are included with the "+" models, like Docker container support, Plex transcoding, etc.
Ideally, he wanted networkable storage, perhaps a Plex server for music, and perhaps consider some of the other Synology provided packages.
The perfect candidate was the Synology DS220j, at $189.99 we considered this to be a very affordable price-point for what he was after.
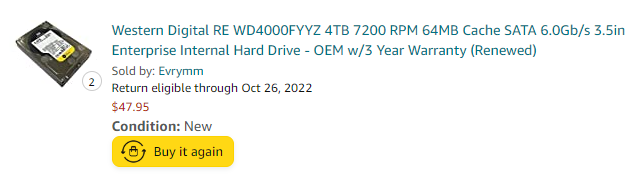
I was able to find him some 4TB WD RE's for $47.95/drive on Amazon, they're pretty good for refurbished drives, and are designed to run 24/7 in a NAS.

It's pretty small, at the size of a toaster, and pretty lightweight in terms of power consumption and noise.

I also took the time to join the NAS to my local AD infrastructure over the IPSec VPN we setup a while back.
This allows for authenticating against AD/LDAP without actually hosting a DC onsite. This assists with keeping maintenance to a minimum. All I have to do is login maybe once or twice a month to update DSM, Plex, and whatever else is installed.
But what about the account issues?
Hold your horses, we're getting there.
After reviewing the information I used to convert my personal account from an AzureAD-only account, I was able to use the following technique convert his account to a "HybridAD account":
A) Create a user in AD matching his username.
B) Add an attribute that binds the AD user to the AzureAD user. (email address)
C) Setup the "proxyAddresses" attribute in AD to match the AzureAD attribute (email address again)
D) Perform a force-sync within AzureAD Sync, and the user should switch from AzureAD to Hybrid in the O365 GUI and be able to authenticate against LDAP. (This may take a few minutes to show up)
The user's device can remain AzureAD joined, and should be able to authenticate against LDAP/AD if the AD sync is setup properly.
This is gone over in great detail in an article I found while researching this again recently, It's hard to describe processes without looking them up sometimes.
After making these changes, he was able to access SMB shares located on the Synology NAS without any issue, as well as now authenticate into any permitted services operating within "HQ" back in STL.
But wait, there's more!
I need a way to remotely manage machines now that they're on my domain, that's like Sysadmin 101.
If you're not familiar with the concept of an MDM, I'll give a crash-course real quick:
Essentially, an MDM (Mobile Device Management) platform is a piece of software designed to manage a fleet of devices. i.e. servers, desktops, laptops, phones, tablets, etc.
MDMs allow an admin to view statistics, remotely manage, and assist users with their machines. Think of it as a second set of hands, if you can't be at an office, the software does the legwork and digitally allows you to assist a user.
I previously used Cisco Meraki as my MDM, but over the years there hasn't been much in terms of improvement on their remote access software. It works, but it has it's flaws, like high latency, pixelating, and random disconnects.
After doing some research on opensource MDMs, I came across TacticalRMM. It's based off of MeshCentral and puts a nicely made UI on top to make it feel more modern.
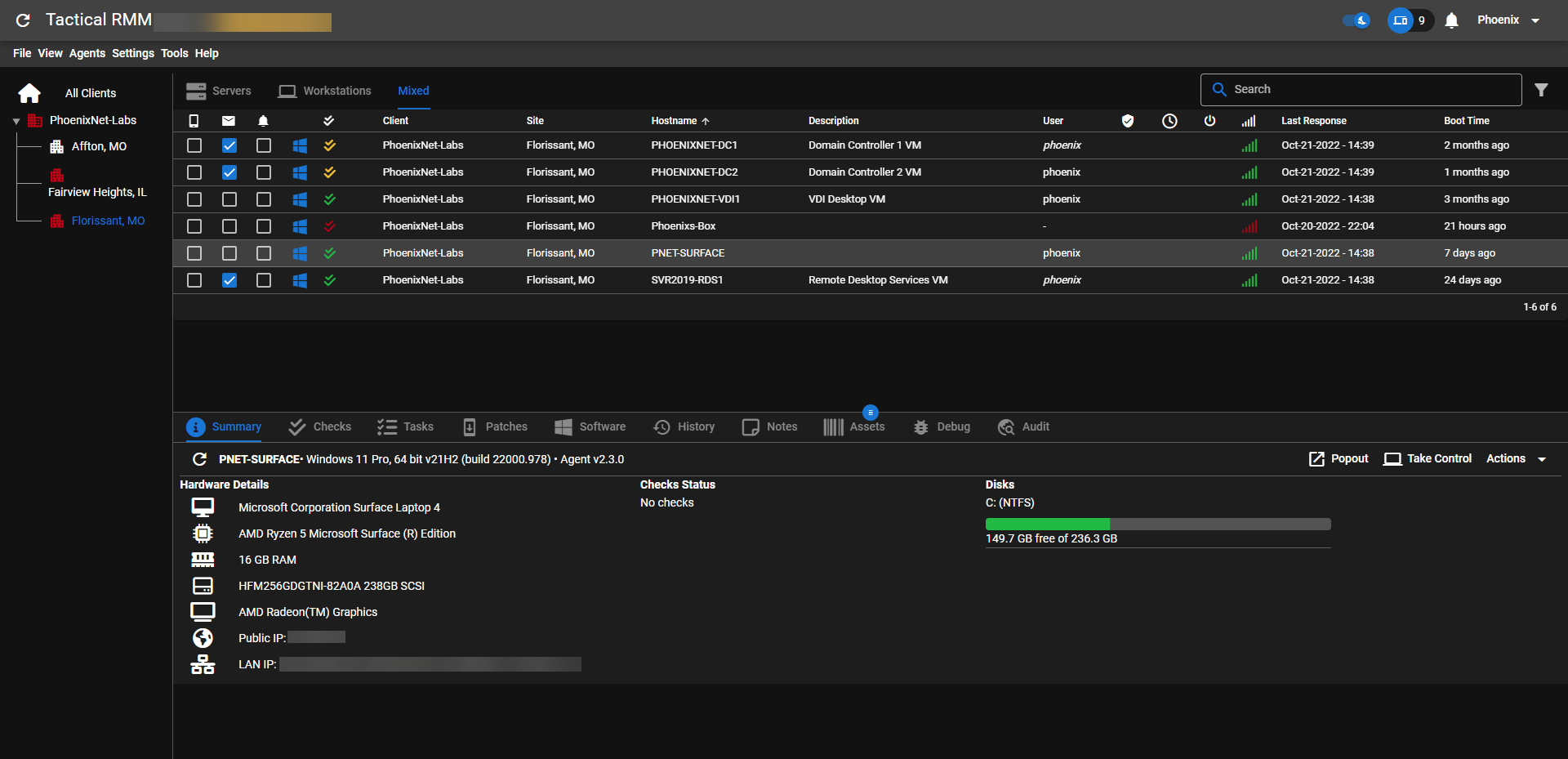
I deployed the MDM on all of my Windows based machines for now (they're working on Linux support soon!) and use it to monitor and assist when needed.
Also, I setup various checks to run daily, including checking for update status, drive status, and various other housekeeping tasks. It auto-alerts me when devices fall out of compliance so that I can take action whenever necessary.
That's it from me for now, I hope you didn't miss me too much, I love writing these articles, but sometimes I just get a little too caught up in life to write them, so sorry if I kept you all hanging!
Until next time!